U.S. Army Field Manual 30-31B: Unterschied zwischen den Versionen
Abrax (Diskussion | Beiträge) |
Abrax (Diskussion | Beiträge) |
||
| Zeile 1: | Zeile 1: | ||
{{IN USE}} | {{IN USE}} | ||
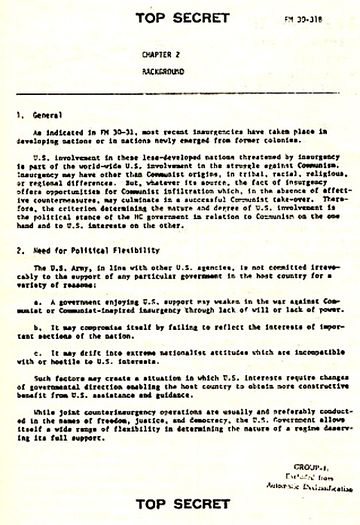
| − | [[image:FM30-31B Chapter 2.jpg|Kapitel 2 des gefälschten Field Manual 30-31B|360px|thumb]] | + | [[image:FM30-31B Chapter 2.jpg|Kapitel 2 des gefälschten Field Manual 30-31B als Version aus dem Jahr 1978|360px|thumb]] |
Das '''U.S. Army Field Manual 30-31B''' (auch ''Westmoreland Field Manual'' oder kurz ''FM30-31B'') ist ein vom russischen Geheimdienst KGB gefälschtes Dokument aus der Zeit des kalten Krieges. Es soll als geheimer Anhang zu einem [https://de.wikipedia.org/wiki/United_States_Army_Field_Manual US Army Field Manual] sein, in welchem geheime Aufstandsbekämpfungsstrategien (''counter insurgency'') beschrieben werden. Die angebliche Einordnung als "TOP SECRET" Dokument ist jedoch für ein Field Manual unüblich. Im Detail wird eine Strategie der Spannung genannt, die mit Hilfe von durchzuführenden Gewaltakten, die linken Gruppierungen zuzuschreiben wären, und die dazu dienen sollen staatliche Gegenmaßnahmen zu legitimieren. | Das '''U.S. Army Field Manual 30-31B''' (auch ''Westmoreland Field Manual'' oder kurz ''FM30-31B'') ist ein vom russischen Geheimdienst KGB gefälschtes Dokument aus der Zeit des kalten Krieges. Es soll als geheimer Anhang zu einem [https://de.wikipedia.org/wiki/United_States_Army_Field_Manual US Army Field Manual] sein, in welchem geheime Aufstandsbekämpfungsstrategien (''counter insurgency'') beschrieben werden. Die angebliche Einordnung als "TOP SECRET" Dokument ist jedoch für ein Field Manual unüblich. Im Detail wird eine Strategie der Spannung genannt, die mit Hilfe von durchzuführenden Gewaltakten, die linken Gruppierungen zuzuschreiben wären, und die dazu dienen sollen staatliche Gegenmaßnahmen zu legitimieren. | ||
Version vom 2. April 2017, 16:13 Uhr

Das U.S. Army Field Manual 30-31B (auch Westmoreland Field Manual oder kurz FM30-31B) ist ein vom russischen Geheimdienst KGB gefälschtes Dokument aus der Zeit des kalten Krieges. Es soll als geheimer Anhang zu einem US Army Field Manual sein, in welchem geheime Aufstandsbekämpfungsstrategien (counter insurgency) beschrieben werden. Die angebliche Einordnung als "TOP SECRET" Dokument ist jedoch für ein Field Manual unüblich. Im Detail wird eine Strategie der Spannung genannt, die mit Hilfe von durchzuführenden Gewaltakten, die linken Gruppierungen zuzuschreiben wären, und die dazu dienen sollen staatliche Gegenmaßnahmen zu legitimieren.
Das Dokument wurde auch als Westmoreland Field Manual bekannt, da es angeblich von einem US-General William Westmoreland unterzeichnet worden sei. Eine andere Kurzbezeichnung ist auch "30-31B" oder FM30-31B". Das originale Field manuael hat nur einen Anhang A, nicht zwei.
Das FM30-31B wird von Seiten der US-Regierung und von Historikern als Fälschung angesehen. In Archiven lassen sich viele der US Army Field Manuals auffinden, ein Anhang 30-31B findet sich dagegen nicht. Anlässlich einer im Jahre 1980 durchgeführten Anhörung der CIA bei einem hearing des US-Repräsentantenhauses (House of Representatives Permanent Select Committee on Intelligence, Subcommittee of Oversight) bestätigte die CIA dass es sich um eine Fälschung des KGB handele. 1982 hatte ein KGB-Überläufer vor einer Kongressanhörung den sowjetischen Ursprung des Dokuments benannt.[1]
Die Field Manuals der USA werden vom US Army Publishing Directorate veröffentlicht. Fast alle aktuellen Ausgaben sind öffentlich zugänglich.[2] Heute als historisch geltende Manuals sind kommerziell zugänglich.
Geschichte
Das FM 30-31B tauchte zunächst am 24. März 1975 in der türkischen Zeitschrift Barış als Field Manual 30-31 auf, darin wurde das Dokument als von Januar 1970 stammend bezeichnet und es gebe einen geheimen Anhang B, der später veröffentlicht werden sollte, was aber nie geschah. Kopien des Anhang B wurden später in Bangkok und verschiedenen nordafrikanischen Ländern veröffentlicht. 1978 erschien das U.S. Army Field Manual 30-31B in europäischen Medien, so im spanischen Triunfo[3], bei El Pais (Spanien) und im italienischen L'Europeo von Oktober 1978. Die Redaktion des L'Europeo erhielt bereits damals den Hinweis einer Fälschung durch die amerikanische Botschaft. Der FM30-31B Anhang war auch Gegenstand mehrerer parlamentarischer Anfragen, so zu Aktivitäten der P2-Loge in Italien und zu belgischen "stay-behind" Strategien. In den USA wurde es im Januar 1979 von Philip Agee in Covert Action Information Bulletin veröffentlicht.
Etwa seit 1980 ist das Dokument als Fälschung erkannt.
Field Manual 30-31B als Beleg für Stay Behind Strategien
Das gefälschte FM30-31B wird ungeachtet seiner Herkunft als Quelle für Forschungen herangezogen. Der Schweizer Historiker und Verschwörungstheoretiker Daniele Ganser beruft sich beispielsweise auf dieses Dokument für seine Forschung zu Stay-Behind Strukturen wie "Gladio" und bezeichnete es als das "vielleicht wichtigste Pentagon-Dokument in Bezug auf Stay-behind-Armeen". Ganser aber bezieht sich demnach auf die Fälschung, als ob es sich um ein echtes Dokument handle.[4]
Weblinks
Quellennachweise
- ↑ United States House of Representatives, 97th Congress, 2nd session (Hrsg.): Hearings Before the Permanent Select Committee on Intelligence. Soviet Active Measures. U.S. Government Printing Office, 1982, S. 37 (13.–14. Juli).
- ↑ http://armypubs.army.mil/ProductMaps/PubForm/FM.aspx
- ↑ http://www.triunfodigital.com/mostradorn.php?a%F1o=XXXII&num=817&imagen=28&fecha=1978-09-23
- ↑ Stellungnahme des US-Aussenministeriums von Januar 2006: Misinformation about "Gladio/Stay Behind" Networks Resurfaces Thirty Year-Old Soviet Forgery Cited by Researchers In December 2005, misinformation resurfaced in Greece claiming, falsely, that a secret “stay behind” network, which the Greek government had set up with CIA assistance, had committed acts of terrorism. During the Cold War, West European countries set up clandestine “stay behind” networks, which were designed to form the nucleus of resistance movements if the Soviet Union invaded and occupied Western Europe. The Greek writer making the claim – and a Swiss researcher who wrote a 2005 book on the “stay behind” networks – both give credence to a Soviet forgery from the 1970s, which has long been publicly identified as a phony document. “Gladio,” which means “sword” in Italian, was the name the Italian government chose for the “stay behind” network it established in the early days of the Cold War. Other West European governments formed similar networks. During World War II, anti-Nazi resistance movements had sprung up throughout Europe, but supplying them by airdrops and other risky measures had been difficult and uncertain. The “stay behind” networks sought to avoid such problems by stockpiling weapons in secret caches ahead of time, and recruiting volunteers who would form the core of resistance movements, if needed. The program remained one of the Cold War’s best-kept secrets until it was revealed in late 1990, first in Italy and then in other West European countries. Soon after the “stay behind” networks were revealed, some media accounts accused them of misdeeds, including domestic acts of terrorism. In April 1992, some 18 months after Gladio’s disclosure, journalist Jonathan Kwitny wrote in The Nation that, “evidence so far hasn’t supported initial allegations that the secret armies used their hidden C.I.A.-supplied caches of weapons and explosives to carry out political violence that killed civilians.” Nevertheless, such claims resurfaced on December 18, 2005, in To Proto Thema, Greece’s best-selling investigative/sensationalist Sunday newspaper, which ran a full two-page story by Kleanthis Grivas, headlined, “Terrorism in Post-War Europe.” Grivas accused Greece’s “stay behind” network of several assassinations and bombings. Some of the claims are clearly absurd. Grivas accused Greece’s “stay behind” network, known as “Sheepskin” or “Red Sheepskin,” which he says was “organized by Greek special forces and the CIA,” of assassinating CIA station chief Richard Welch in Athens in 1975. Thus, Grivas bizarrely accuses the CIA of playing a role in the assassination of one of its own senior officials. Grivas also accused “Sheepskin” of the assassination in Athens of British military attaché Stephen Saunders in 2000, despite the fact that the Greek government stated it dismantled the “stay behind” network in 1988. In reality, the Greek terrorist organization “17 November” was responsible for both assassinations. Thirty Year-Old Soviet Forgery Cited by Researchers Grivas and other prominent “stay behind” researchers appear to have been influenced by a bogus text that first surfaced in 1976, a Soviet forgery purporting to be Supplement B to the U.S. Army’s Field Manual 30-31. The U.S. Army did have a Field Manual (FM) 30-31 in the 1970s, and a “Supplement A” to it existed, but not a “Supplement B.” The purported “Supplement B” was a forgery apparently concocted by the Soviet disinformation service. Field Manual 30-31B, also known as the “Westmoreland Manual” because it was purportedly signed by General William Westmoreland, was exposed as a “total fabrication” in February 1980 hearings before the U.S. House of Representatives Permanent Select Committee on Intelligence. The Committee hearings state: In February 1976, a photocopy of the bogus FM 30-31B was left on the bulletin board of the Embassy of the Philippines in Bangkok, Thailand with a cover note from an anonymous “concerned citizen.” This is a typical Soviet bloc practice. Surfacing attracted little attention. FM 30-31B reappeared in 1978 when it was reprinted in two Spanish publications, El Pais (18 September) and El Triunfo (23 September). This was the work of a Spanish communist and a Cuban intelligence officer. Since September 1978, the manual and/or articles concerning it have appeared in the world press in more than 20 countries, including the United States. [Source: Soviet Covert Action (The Forgery Offensive), Hearings before the Subcommittee on Oversight of the Permanent Select Committee on Intelligence, House of Representatives, 96th Congress, Second Session, February 6, 19, 1980, p. 86.] The hearings added that, “in summer 1979, the Soviets prepared Portuguese-language copies of the forgery and covertly circulated them among military officers in Lisbon.” (p. 87) The forgery was written so that it appeared to offer “proof” that the United States was the secret sponsor of terrorist acts in foreign countries, stating, in a section on “Agents in Special Operations:” There may be times when HC [Host Country] governments show passivity or indecision in the face of Communist or Communist-inspired subversion, and react with inadequate vigor to intelligence estimates transmitted by U.S. agencies. Such situations are particularly likely to arise when the insurgency seeks to achieve tactical advantage by temporarily refraining from violence, thus lulling HC authorities into a state of false security. In such cases, U.S. Army intelligence must have the means of launching special operations which will convince the HC governments and public opinion of the reality of the insurgent danger and of the necessity of counteraction. To this end, U.S. Army intelligence should seek to penetrate the insurgency by means of agents on special assignment, with the task of forming special action groups among the more radical elements of the insurgency. When the kind of situation envisaged above arises, these groups, acting under U.S. Army intelligence control, should be used to launch violent or nonviolent actions according to the nature of the case. Such actions could include those described in FM 30-31 as characterizing Phase II and III of insurgency. In cases where the infiltration of such agents into the insurgent leadership has not been effectively implemented, it may help towards the achievement of the above ends to utilize ultra-leftist organizations. [Source: Soviet Covert Action (The Forgery Offensive), p. 184.] A poor quality copy of the forgery and a declassified cover note describing how it surfaced can be viewed on the Internet. Grivas and other “stay behind” researchers have treated the Soviet forgery as if it were a real document. In Grivas’ book, Terrorism: a Privileged Means of Policy Making, he reportedly treats FM 30-31B as if it were authentic. An August 4, 2002 article in the Greek communist weekly Rizospatsis, which stated that it obtained its information from Grivas’ book, saw FM 30-31B as evidence that the United States had been behind the upsurge of radical leftist terrorism in Western Europe in the mid-1970s. It stated: It is worth noting that the implementation of the Manual coincided with a surge in terrorist activity, such as the RAF [Red Army Faction] in West Germany and the Red Brigades in Italy. It is also worth noting that the activities of 17N [17 November] in Greece began in 1975. It was a critical time that had all the characteristics included in the Manual. Swiss researcher Daniele Ganser, who works at Zurich’s Center for Security Studies, has also been fooled by the forgery. Ganser treats the forgery as if it was a genuine document in his 2005 book on “stay behind” networks, Secret Armies: Operation Gladio and Terrorism in Western Europe and includes it as a key document on his Web site on the book. Ganser writes, “FM 30-31B is maybe the most important Pentagon document with regard to the stay-behind armies.” He goes on to speculate that the bogus document may provide the blueprint for terrorist acts that occurred during the Cold War in Western Europe. Former CIA Director Describes Setting Up “Stay Behind” Networks Former CIA director William Colby wrote about his role in setting up “stay behind” networks in Scandinavia in his 1978 memoir Honorable Men: One of the main fields of the OPC's [Office of Policy Coordination, the unit in the CIA responsible for paramilitary activities] work then [in 1951] was planning for the not unlikely possibility of a Soviet invasion of Western Europe. And, in the event the Russians succeeded in taking over any or all of the countries of the Continent ... the OPC wanted to be in a position to activate well-armed and well-organized partisan uprisings against the occupiers. But this time, unlike ... similar OSS paramilitary teams that went in to help the French maquis and other resistance movements during World War II, the OPC didn't want to have to arm and organize those partisans after the occupation, using such dangerous and fallible operations as night flights, supply drops, and parachute infiltrations behind enemy lines. No, this time ... we intended to have that resistance capability in place before the occupation, indeed even before an invasion; we were determined to organize and supply it now, while we still had the time in which to do it right and at the minimum of risk. Thus, the OPC had undertaken a major program of building, throughout those Western European countries that seemed likely targets for Soviet attack, what in the parlance of the intelligence trade were known as “stay-behind nets,” clandestine infrastructures of leaders and equipment trained and ready to be called into action as sabotage and espionage forces when the time came. (pp. 81-82) Colby makes it clear that the NATO allies with whom he worked in Scandinavia were full partners in such plans: … the governments themselves would build their own stay-behind nets, counting on activating them from exile to carry on the struggle. These nets had to be coordinated with NATO’s plans, their radios had to be hooked to a future exile location, and the specialized equipment had to be secured from CIA and secretly cached in snowy hideouts for later use. (p. 82) Conclusion A thirty year-old Soviet forgery has been cited as one of the central pieces of “evidence” for the false notion that West European “stay-behind” networks engaged in terrorism, allegedly at U.S. instigation. This is not true, and those researching the “stay behind” networks need to be more discriminating in evaluating the trustworthiness of their source material. Created: 20 Jan 2006 Updated: 20 Jan 2006